Personal information should be managed as part of the data used by the organization. It
should be managed from the time the information is conceived through to
its final disposition.Protection of personal information should consider the impact of the
cloud on each of the following phases as detailed in Figure 1.
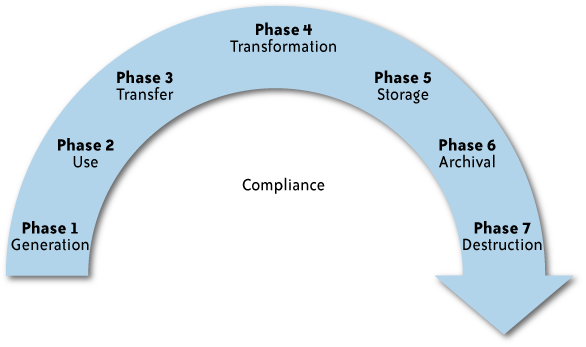
The components within each of these phases are:
Generation of the information
Ownership: Who in the organization
owns PII, and how is the ownership maintained if the
organization uses cloud computing?
Classification: How and when is PII
classified? Are there limitations on the use of cloud computing
for specific data classes?
Governance: Is there a governance
structure to ensure that PII is managed and protected through
its life cycle, even when it is stored or processed in a cloud
computing environment?
Use
Internal versus external: Is PII used
only within the collecting organization, or is it used outside
the organization (e.g., in a public cloud)?
Third party: Is the information
shared with third parties (e.g., subcontractors or CSPs)?
Appropriateness: Is the use of the
information consistent with the purpose for which it was
collected? Is the use within the cloud appropriate based on the
commitments the organization made to the data subjects?
Discovery/subpoena: Is the
information managed in the cloud in a way that will enable the
organization to comply with legal requirements in case of legal
proceedings?
Transfer
Public versus private networks: When
information is transferred to a cloud is the organization using
public networks, and is it protected appropriately? (PII should
always be protected to address the risk level and legal
requirements.)
Encryption requirements: Is the PII
encrypted? Some laws require that PII will be encrypted when
transmitted via a public network (and this will be the case when
the organization is using a public cloud).
Access control: Are there appropriate
access controls over PII when it is in the cloud?
Transformation
Derivation: Are the original
protection and use limitations maintained when data is
transformed or further processed in the cloud?
Aggregation: Is data in the cloud
aggregated so that it is no longer related to an identifiable
individual (and hence is no longer considered PII)?
Integrity: Is the integrity of PII
maintained when it is in the cloud?
Storage
Access control: Are there appropriate
controls over access to PII when stored in the cloud so that
only individuals with a need to know will be able to access
it?
Structured versus unstructured: How
is the data stored to enable the organization to access and
manage the data in the future?
Integrity/availability/confidentiality:
How are data integrity, availability, and confidentiality
maintained in the cloud?
Encryption: Several laws and
regulations require that certain types of PII should be stored
only when encrypted. Is this requirement supported by the
CSP?
Archival
Legal and compliance: PII may have
specific requirements that dictate how long it should be stored
and archived. Are these requirements supported by the
CSP?
Off-site considerations: Does the CSP
provide the ability for long-term off-site storage that supports
archival requirements?
Media concerns: Is the information
stored on media that will be accessible in the future? Is the
information stored on portable media that may be more
susceptible to loss? Who controls the media and what is the
organization’s ability to recover such media from the CSP if
needed?
Retention: For how long will the data
be retained by the CSP? Is the retention period consistent with
the organization’s retention period?
Destruction
Secure: Does the CSP destroy PII
obtained by customers in a secure manner to avoid potential
breach of the information?
Complete: Is the information
completely destroyed? Does the destruction completely erase the
data, or can it be recovered?
The impact differs based on the specific cloud model used by the
organization, the phase (Figure 7-1, shown
earlier) of personal information in the cloud, and the nature of the
organization. The following analysis provides some of these
considerations; however, every organization should consider performing a
Privacy Impact Assessment (PIA) before embarking on a cloud computing initiative that
involves personal information.